Election Hacking: Facts Versus Fears
By Peter Cockshott

October 19, 2020 Technology
Free and fair elections are a cornerstone of American democracy. In recent years, however, voting has been at the center of discussions about computer fraud, primarily concerning the 2016 and 2020 U.S. presidential elections. Amid the glut of clickbait headlines and misleading articles, it can be difficult to get a direct answer to the question: Is the integrity of U.S. presidential elections at risk of election hacking? By examining the voting process and supporting technologies, we can better understand the potential for adversaries to affect elections and shed light on what security controls best mitigate these risks.
Voting overview
On the surface, the voting process is straightforward: Voters register, voters cast ballots, votes are counted, results are submitted, results are tallied (and temporarily retained for audit purposes), and winners are declared. However, this process is riddled with opportunities for malicious parties to tamper with voting equipment (and voters themselves) and potentially alter election results.
Before addressing any technical vulnerabilities that exist in this process or with voting machines, it’s important to understand the different types of voting machines in use at polling stations across the United States.
- Direct recording electronic (DRE) systems record votes via touchscreen or mechanical buttons directly into computers’ memory components. The computers store the voters’ choices on a removable cartridge or a hard drive, or choices are printed to paper. The votes, whether in electronic or paper format, are then tabulated and retained so that they can be counted in case of an audit or an election recount.
- Ballot marking device (BMD) systems typically use touchscreens, audio, or other accessibility features to help disabled voters record their votes. Rather than recording the vote into the computer’s memory, voters mark physical ballots, which are later tabulated.
- Punch card voting is the classic method by which a voter punches a hole in a paper card to indicate his or her vote. The ballot is then placed in a sealed, tamper-proof box to be tabulated manually or scanned by a computer later.
- Optical scanners are among the most common methods of tabulating results from polling stations with paper ballots. They work by scanning paper ballots that voters have marked by filling in an oval, box, or similar shape. Typically, the paper ballots are scanned either at the polling place or at a centralized location for audit purposes.
Polling stations across the United States employ a range of methods. (See Verified Voting’s data set for an overview of the entire country’s voting methods and corresponding breakdown of equipment by district.) Despite the variety of available machinery, Verified Voting’s data indicates that the overwhelming majority of precincts across the country use hand-marked, paper ballots counted by optical scanners and provide the option for voters to use a BMD system for accessibility purposes.
Ethical hackers
So, how do criminals and foreign adversaries try to take advantage of vulnerabilities in voting computers and election counting machines? Enter DEF CON, one of the premier information security conferences at which members of the ethical hacking community share offensive security ideas, tools, and methodologies. Since 2017, DEF CON has sponsored a Voting Machine Hacking Village to identify election infrastructure vulnerabilities and to propose solutions that would strengthen voting machinery. Voting Village events involve gathering an assortment of voting machines assembled by different manufacturers and researching vulnerabilities that might exist on the devices. DEF CON has also invited election officials and manufacturers to participate in the exercises, sometimes with mixed results.
The devices in the Voting Village range from DRE voting machines and electronic poll books to BMD voting machines, optical scanners, and hybrid systems that combine various methods. The 2019 DEF CON Voting Machine Hacking Village report noted that village participants were capable of “compromising every one of the devices in the room in ways that could alter stored vote tallies, change ballots displayed to voters, or alter the internal software that controls the machines.” Write-ups of each machine’s vulnerabilities included in the DEF CON report provided some alarming details regarding the security of these devices: unrestricted ports (such as USB, RJ45, and CF), plain-text encryption keys being stored in an XML file, no BIOS passwords set (allowing an attacker the ability to change the boot order and other system settings), unencrypted hard drives, unnecessary software being installed on many of the devices (including web browsers and default bloatware, such as Netflix), default credentials, and susceptibility to attacks based on denial of service (DoS), which could be used to prevent voters from participating.
While some of these tests were conducted in lab environments that didn’t replicate election booth conditions, many of the discovered vulnerabilities could be covertly exploitable under typical election conditions. It should be noted that hacking voting machines is most likely not the ideal method of attack for foreign adversaries because they would need physical access to the machines, as the vast majority of the voting machines are not connected to the internet. This type of attack is also difficult to perform at scale, as it would require a physical presence at a large number of voting sites without being detected.
Foreign adversaries
Ethical hackers and researchers are not the only ones finding and exploiting vulnerabilities in election equipment. A Senate intelligence report found that a Russian military intelligence group compromised the Illinois state election infrastructure in June 2016 – less than six months before the presidential vote that same year. Later, an indictment of 12 Russian intelligence officials alleged that the records of roughly 500,000 Illinois voters were compromised from the Illinois State Board of Elections (IL SBE), including information such as voters’ full names, addresses, partial Social Security numbers, dates of birth, and driver’s license numbers.
Most disturbing about this attack was that the primary exploit used to gain a foothold to the IL SBE network was a structured query language injection (SQLi) attack, a type of attack that has been known about since at least 1998 and is easily identifiable via vulnerability scanning tools and penetration assessments. SQLi attacks are specially crafted SQL queries submitted to input fields (such as one of the voter verification fields on the IL SBE website) that can allow remote attackers to run queries. These queries can allow attackers to search data, delete data, edit data, exfiltrate data from the target databases, and (in this instance) become system administrators. According to Steve Sandvoss, the executive director of the IL SBE, an adversary group had been in the IL SBE network for three weeks undetected before launching its attack, which compromised the full records of 3,500 Illinois voters and partial records of roughly 500,000.
The Senate intelligence report noted that by late September 2016, the Cyber Analysis Division within the Department of Homeland Security’s Office of Intelligence and Analysis had “determined that internet-connected election-related networks in 21 states were potentially targeted by Russian government cyber actors.” The report also indicated that developments in 2018 supported the notion that all 50 states were targeted, though no evidence exists that any voting machines were compromised or that votes were changed in any way during the polling process.
Voter data
In a “60 Minutes” interview, Michael Daniel, former cybersecurity coordinator and special adviser to President Barack Obama, stated that “it was always our working assumption that we did not detect all of the potential Russian activity that was going on.” Most voters might wonder what effects such interference – known and unknown – could have on an election. Even if voting machines remained safe and untampered with, what could attackers do with this type of access and information?
Daniel explained what basic manipulations to a voter registration database could lead to during crucial election periods: “What seemed much more likely to us was causing chaos at the polls on election day.” To cause chaos, a foreign adversary could “intrude into a voter registration database, and…change two digits of everybody’s address so that their voter ID doesn’t match what’s in the voter rolls when they show up at the polls.” In this regard, the attack acts as a DoS attack method in which voters would be delayed or prevented from voting because of issues with their registration information.
While an isolated instance of this would be frustrating, this type of attack is scalable due to the nature of the state voter registration databases. Amplifying this attack would be similar to performing a distributed DoS attack in which polling stations across the U.S. would simultaneously experience issues with their states’ voter registration information and might not be able to process voters efficiently. Criminals could also use voter registration information to perform identity theft, create targeted phishing lists, or prevent some voters from receiving their absentee ballots.
Alternatively, attackers could attempt to use the database access to gain authentication on a state election official’s corporate network, elevating their network privileges and potentially pivoting into other state agency networks. In doing any of these things, a foreign adversary could sow doubt about the integrity of the U.S. election process, discourage voters from participating in elections, or further compromise U.S. voting infrastructure.
Voting infrastructure
These types of attacks demonstrate that it’s not just the voting machines that need to be secured but also the underlying infrastructure of voting machine manufacturers, state election infrastructure, and the supply chain security of the voting machines.
One example that highlights the risks in this area occurred in 2020, when a security researcher compromised the corporate virtual private network of one large voting machine manufacturer. While the compromise occurred as part of an ethical security review under the company’s newly developed disclosure program, it’s unclear how long this vulnerability might have existed before being identified and remediated.
In addition to this manufacturer, seven others have registered with the U.S. Election Assistance Commission (EAC) and met its testing and certification program requirements. These manufacturers are required to demonstrate that their facilities and products adhere to the EAC’s security standards, but some are concerned that meeting the standards isn’t enough, and that problems might start during development, further down the supply chain.
Supply chain risks
The variety of voting machines and manufacturers does indeed complicate securing the development of voting machines and software. The Brennan Center for Justice at NYU Law noted that, despite the EAC’s authority to conduct manufacturing site visits through its Quality Monitoring Program, the EAC’s authority covers only the voting systems that are submitted for voluntary certification and does not cover the full spectrum of vendor products and services. “There is no federal scrutiny of supply chains for components sourced for noncertified products and services,” a Brennan Center for Justice report notes. Neither are there “requirements that vendors report breaches, screen employees’ backgrounds, patch security flaws, report foreign ownership or control, or ensure the physical security of sensitive software and hardware.”
Currently, no widely publicized instances of tampering with voting equipment in the supply chain have been publicly disclosed, but that doesn’t mean this attack method is theoretical. In his 2014 book on the subject, journalist and author Glenn Greenwald referred to an allegedly leaked report from the head of the National Security Agency’s (NSA) Access and Target Development Department that detailed the NSA operations to intercept “U.S.-made hardware, embedding backdoor surveillance tools, then repackaging the equipment and sending it onto international customers.”
By compromising another nation’s infrastructure hardware while it is in transit, the NSA can gain access to air-gapped systems, which are systems that are physically isolated from the internet and other machines. If a foreign adversary, such as China, were able to similarly intercept domestic-made hardware used in U.S. voting machines (such as the surface mounts, capacitors, resistors, inductors, and other devices sourced from China-based manufacturers for U.S. machines) and install backdoors or otherwise tamper with the devices, it could affect the confidentiality, integrity, or availability of the voting process.
Voting equipment supply chain remains an area in which further federal oversight is needed, and supply chain audits should be performed to determine if organizations in the supply chain have implemented information security governance programs and compensating controls to reduce risks to acceptable levels. However, as with voting machine attacks, voting machine supply chain tampering would also require a physical presence and is therefore also a less likely attack vector.
Voting by mail
Because of the pandemic, voting by mail will take a much more prominent role in the 2020 election. Does the pandemic provide yet another potential avenue for attackers to disrupt or otherwise compromise the voting process?
To vote by mail, voters must submit a request for ballots by providing their full names and addresses to the local election authorities. Upon verification of the voter’s information by matching the submitted data to voter registration information, the local election authority provides the individual with a ballot and either one or two return envelopes. The ballot is meant to be placed in the outer envelope, which the voter must sign. The signature on the outside envelope is matched with the signature on the voter registration records to confirm authenticity before being removed. The ballot, sometimes contained within an additional inside envelope to help maintain impartiality in the counting process, is then processed – though the results are not yet counted until the polls close on election night.
Alternatively, voters can drop off their ballots at state-designated sites in secured drop boxes. Some of these sites are temporary, staffed lockboxes, and others are permanent, unstaffed drop boxes that are available any time of the week. According to the EAC, “Only an election official or a designated ballot drop box collection team should have access to the keys and/or combination of the lock. In addition to locks, all drop boxes should be sealed with one or more tamper evident seals.” In ideal circumstances, unstaffed 24-hour drop boxes would be placed in the line of sight of surveillance cameras and in well-lit, high-traffic areas. The overall process generally looks like the following:
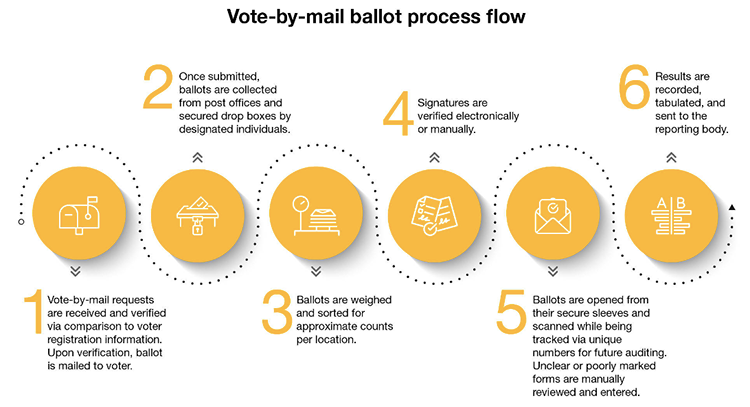
Source: Crowe analysis
Some of the same risks inherent in traditional voting methods apply to voting by mail, such as incorrect voter data in voter registration rolls and databases. As previously mentioned, if a criminal has the capability to modify voter registration information such as addresses or signatures, doing so could significantly delay the voter verification process, which could render some voters unable to submit their mail-in ballots on time. If a voter signature is not provided or cannot be verified by local election officials, the officials will work with the voter to resolve the issue either by resending the secure envelopes or requesting updated voter records. Unfortunately, if there is no time to verify a new signature or resubmit the mail-in ballot, the vote is discounted altogether.
National Public Radio’s July 2020 analysis of primaries conducted to that point in the year indicated that at least 65,000 voters’ ballots were discarded or rejected because they did not arrive on time. This number accounts for roughly 1% of the vote in most states – enough to potentially alter the outcome of a close election. Not only does voting by mail place stress on the already struggling United States Postal Service (USPS) to quickly and appropriately process ballots, but it also underscores the importance of the USPS’ infrastructure security in the integrity of the election process.
Unfortunately, the USPS has been the subject of several high-profile information security breaches. Two of the most notable incidents are illustrative. In 2018, the USPS site had a vulnerability that allowed any user with a usps.gov account to view (and in some cases modify) account details for 60 million other users. In 2014, personally identifiable information (including Social Security numbers) for roughly 750,000 active and retired USPS employees was compromised, as was data on 2.9 million USPS customers. While these breaches were a far cry from accessing mail sorting information systems or other infrastructure critical to mail processing, they do raise questions about the USPS security posture and the feasibility of compromising those systems.
Vote-by-mail ballot security
In addition, concerns exist regarding the inconsistent secure storage of mail-in ballots and the use of drop boxes. In general, while ballots that have been sent via mail await processing, they are stored in secured areas at the local election official’s designated site with tamper evident seals that have a corresponding log entry, which is audited during processing in order to detect any inappropriate or unauthorized access. The EAC has provided guidance on the physical security controls that should exist at these sites, but some believe implementation of physical security controls could be inconsistent.
These concerns were amplified by a lawsuit the Trump campaign filed in the U.S. District Court of Pennsylvania alleging that election officials failed to appropriately monitor or otherwise secure their election drop boxes. The lawsuit requested the ban of “the return of absentee and mail-in ballots to locations other than the respective offices of the county boards of elections.” Despite the EAC’s guidance that the ballot drop boxes should be stored in locations with the appropriate security controls, inconsistencies exist among state implementations because of the increased need to present widely accessible voting methods to all voters, despite the range in resources that districts across the country might have available.
People: The weakest link
As is frequently the case in information security, an adversary’s most likely attack vector is not processes or technology but people. Why? Because unlike processes or technology, people can’t simply be patched or hardened against security standards.
Spear-phishing campaigns – social engineering attacks specifically crafted for target individuals – can be used to infiltrate state election systems or the USPS with the goal of disrupting the voting process. But a more sinister threat exists. Disinformation campaigns, such as those launched by Cambridge Analytica in the 2016 U.S. presidential election, can be used to spread slanderous claims on social media platforms like wildfire. Not only can these disinformation campaigns sway key swing-state voters who might be on the fence, but they can even incite violence and further animosity among political parties.
Unfortunately, these types of attacks are difficult for government entities to defend against because governments have minimal control over social media platforms, many of which do not remove false or misleading posts. Determining whether or how to prevent this type of voter manipulation is wrapped up in debates about free speech versus the responsibilities of platform owners to protect against disinformation. According to sources gathered by the Fordham Law Review, “Social media allows political actors to overwhelm users and disrupt their sense of reality by disseminating false news and political ads to an unprecedented degree at unprecedented speeds.” However, the reality is that “[a]lthough fake news presents a number of threats to democracy, it is protected by the First Amendment.”
In the end, the onus of responsibility to make informed decisions based on fact falls on voters. Voters should seek information on candidates from multiple, verified sources to minimize subjective biases, and they should advocate for social media platforms to do a better job of identifying and blocking disinformation campaigns.
The importance of accurate sources
While many people, the president included, have expressed doubts about the integrity of the vote-by-mail process by claiming that the opportunity for fraud is much greater than with the traditional voting process, it is important to focus on the facts: Intelligence officials have not yet seen evidence of large-scale voter fraud as a result of weaknesses in mail-in voting, nor have intelligence officials seen instances of widespread voter fraud as a result of a voting machine compromise. These determinations are made in part based on post-election audit checks to test the validity of election results (by testing samples of votes across the country and matching them with the paper-audit trail) to verify that votes were not exposed to system glitches or fraud.
So, is the U.S. election process fundamentally flawed and prone to exploitation? Yes and no. While opportunities for the exploitation of vulnerabilities exist throughout the voting process, it is unlikely that a large-scale attack could succeed without detection. Because many of the information systems directly involved in the voting process are kept offline, physical attacks would be difficult to successfully carry out at scale. Simultaneously, state election officials are getting better at securing their infrastructure with the assistance of federal agencies (such as the Cybersecurity and Infrastructure Security Agency) and detailed guidance provided by organizations like the National Institute of Standards and Technology and the EAC. Together these agencies have the capability to make sure that information systems involved in the voting process maintain their integrity.
Unfortunately, based on publicly available evidence, the most urgent risk – and the easiest to exploit – is the spread of disinformation to influence voter behavior. Hopefully, as media distributors continue to implement mechanisms to detect false or misleading claims, voters will continue to evaluate accurate sources and form independent opinions. While past results are not always a reliable indicator for the future, they do provide evidence that the technology involved in the voting process is generally tamper resistant and deserving of a vote of confidence.
For more content like this, click here.

